Email-based social engineering threats are thriving as attackers continue to adapt and evolve their tactics to increase their chances of success.
Email-based social engineering threats are thriving as attackers continue to adapt and evolve their tactics to increase their chances of success.
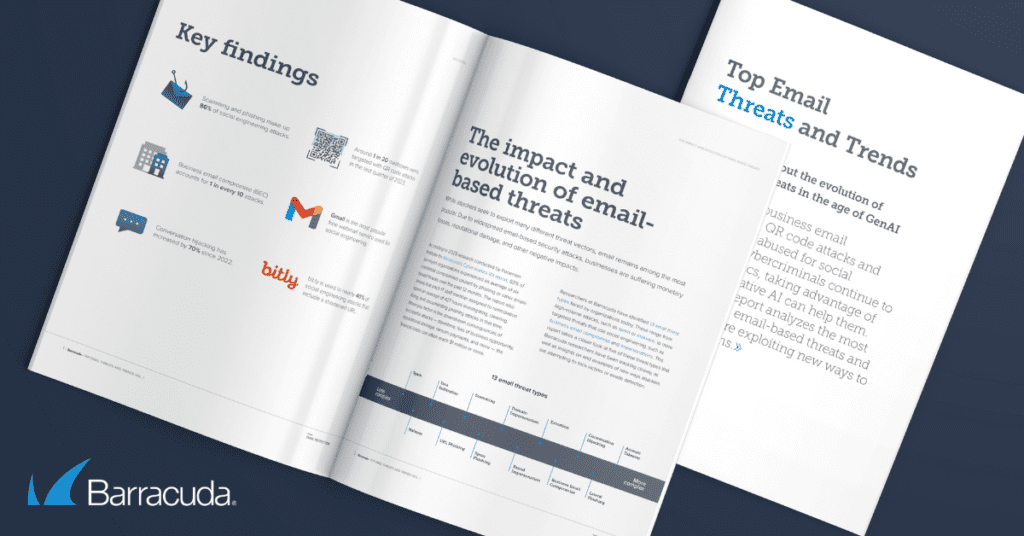
The latest analysis of email detection data by Barracuda researchers reveals that while the landscape remains dominated by mass phishing and general scamming attacks, there’s a steady rise in more targeted, and potentially more damaging threats such as business email compromise and conversation hijacking.
The researchers analyzed 69 million email attacks across 4.5 million mailboxes over a year. The findings are summarized in the new Email Threats and Trends Report vol. 1, which shows that attackers are leveraging the capability of generative AI to scale and tailor their attacks, and implementing QR codes, web shortening links, and webmail to disguise their true nature and intent.
Among other things, the report shows that:
- Business email compromise (BEC) attacks made up 10.6%, or more than 1 in 10, of social engineering attacks in 2023, and the numbers show a steady increase over time. BEC attacks accounted for 8% of attacks in 2022 and 9% in 2021.
- Conversation hijacking made up 0.5% of the social engineering attacks in the past year, an increase of almost 70% compared to 0.3% in 2022. Conversation hijacking attacks require a lot of effort to execute, but the payouts can be significant.
- Phishing accounted for a third (35.5%) of social engineering attacks last year. These generally untargeted, mass attacks try to trick victims into clicking on a phishing link. Phishing emails have been used by attackers for years, and they remain worryingly successful. The Data Breach Investigation Report, 2024 found that it took on average less than 60 seconds for someone to fall for a phishing scam.
- Around 1 in 20 mailboxes were targeted with QR code attacks in the last quarter of 2023. QR code attacks are difficult to detect using traditional email filtering methods. They also take victims away from corporate machines and force them to use a personal device, such as a phone or iPad, which isn’t protected by corporate security software.
- Gmail was the most popular free webmail service used for social engineering. In 2023, Gmail accounted for 22% of the domains used for social engineering attacks, according to Barracuda’s data. Just over half the detected Gmail attacks were used for BEC attacks.
- bit.ly was used in nearly 40% of social engineering attacks that include a shortened URL. URL shorteners condense the link, so the actual link of the site becomes obscured with random letters or numbers. Using this tactic can disguise the true nature and destination of the link.
People are vulnerable targets for social engineering
Last year, just over two-thirds (68%) of data breaches involved a ‘non-malicious’ human element — in other words, an ordinary employee just trying to get on with their job who was caught unawares.
Social engineering attacks from BEC and conversation hijacking to extortion, phishing, scamming and spam need to be taken seriously and either blocked at the gate or quickly contained, neutralized, and eliminated if they make it through.
This is not just about having the right security tools, policies, and programs in place — although that remains critical. IT and security professionals need to understand how the email threat ecosystem is evolving and what this means for the organization and its employees in terms of risk, resilience, and incident response.
Note: This was originally published at Journey Notes.