
Rising AI cost concerns create opportunities for MSPs
As the number of tokens consumed by artificial intelligence (AI) agents and applications continues to climb, organizations are paying much closer attention to cost. It feels like the conversation has shifted almost overnight. Not long ago, the focus was on...

IoT threats in 2026: The blind spot MSPs can’t afford to ignore
Cybersecurity experts have warned about IoT threats for years. But as the IoT security landscape continues to expand and evolve, so do the risks—making this a topic worth revisiting. While solutions to secure IoT devices exist, MSPs must stay immersed...

What competitor websites tell you about service gaps in the market
Here is something I have noticed after years of helping MSPs build outbound sales programs: most of them think they know their competitors. They really don’t. What they have is a collection of impressions: Some gossip from a disgruntled sales...

Tip Tuesday: Use Global MSP Day to set 5 powerful goals for the coming year
When you’re a managed service provider (MSP), it’s easy to get caught up in the day-to-day tasks. Soon, the broader picture gets pushed aside as your team remains stuck in day-to-day operations. As we head into the 9th Annual Global...
Sales & Marketing

Make Global MSP Day more than a hashtag
Posting the hashtag and calling it done is not a marketing strategy. Global MSP Day is a real opportunity sitting on your calendar, and most MSPs will waste it. They’ll post something generic, maybe tag a vendor or two, and...

The hidden AI marketing problem in the MSP industry
AI authority is accumulating in the wrong place. Over the last 30 days, Fox & Crow Group looked at hundreds of LinkedIn posts mentioning AI across MSPs, cybersecurity firms, consultants, vendors, and IT channel participants. What we found was interesting. ...

What Your MSP competitors reveal (and how to sell against it)
Most MSPs doing competitive research are looking at the wrong things. Follower counts. Engagement rates. Whether a competitor posted three times last week or once. Some of this is useful information – an up-to-date, active social media presence can immediately...
Security

Password managers: Your greatest defense or biggest weakness?
Passwords remain a cybersecurity mainstay, surviving despite years of predictions about their demise. Even with constant warnings from security professionals, users still rely on weak choices—like a dog’s name or home address. So, what is an MSP to do? For...

The AI-cybersecurity connection MSPs can’t afford to ignore
One thing is becoming clear for managed service providers (MSPs): future growth will be driven by artificial intelligence (AI) and cybersecurity. More importantly, AI is accelerating demand for cybersecurity services. A recent survey conducted by the Global Technology Industry Association...

The rise of the part-time hacker
Hackers have always run the gamut—from the college kid in his parents’ basement to the nation-state in a sophisticated bunker. There has always been a gap between what an individual hacker could accomplish and what a well-funded nation-state could achieve....
Better Business

Happy Global MSP Day! Today is all about you
Happy Global MSP Day! Today is all about you: the MSPs who keep businesses secure, running and ready for what’s next. Behind every resilient organization, every secure environment and every successful digital transformation, there’s an MSP making it happen. And in 2026, your role has never been more critical. ...

Global MSP Day 2026: Honoring the impact of MSPs worldwide
On June 10, 2026, MSPs around the world will come together for the 9th annual Global MSP Day—a celebration of the innovation, resilience, and impact you drive every day. From defending businesses against ever-evolving threats to unlocking growth through smarter...

Inside IT: Opportunities MSPs should miss
A global survey of 400 IT leaders provides some significant insights into the types of IT expertise that organizations might be willing to consider relying on a provider of IT services to provide. Conducted by the Linux Foundation, the survey...
Tech Insight

Pioneers in Tech: Happy birthday, Telle Whitney!
A very happy birthday to Telle Whitney, whose experiences as a female computer scientist in 1980s and 1990s Silicon Valley inspired work that has made her one of the foremost champions for women in the tech industry. Born June 5,...
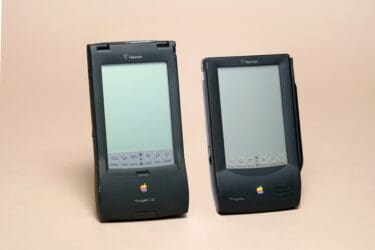
Tech Time Warp: An honest look back at the Apple Newton
The history of Apple is filled with greatest hits—but even its rare misses are worthy of retrospective examination. Take the Apple Newton, which received its first public demo on May 29, 1992, in Chicago at the Consumer Electronics Show. By...

Tech Time Warp: Was Java too much of a good thing?
This edition of Tech Time Warp takes us back to 1995—the public debut of Java, the legendary “Write Once, Run Anywhere” programming language—and a textbook example of the security perils of ubiquitous technology. The birth of Java On May 23,...





