 Small to medium-sized businesses often struggle with identity management because they lack the resources of big companies to implement enterprise solutions, but something as simple as two-factor authentication can help keep your company secure.
Small to medium-sized businesses often struggle with identity management because they lack the resources of big companies to implement enterprise solutions, but something as simple as two-factor authentication can help keep your company secure.
Two-factor authentication simply means that after entering your password, you need to do something else like enter a code that gets texted or emailed to you, or confirm the change with an authentication service.
Of course, you want the individual’s identity to be secure, but at the same time you don’t want to be overly complex. I’ve worked for a large organization that signs me out every couple of weeks, then forces me through a burdensome process that starts with sending a code to my phone.
After I enter the code, I need to come up with a new 20-character password, which can’t be like any of my previous passwords. Then, I have to enter the password twice and make them match. Once I’m able to make that work, which usually takes a couple of shots at least because getting 20-character passwords to match takes some doing, I need to approve the change on my smartphone.
If that sounds like a bit of an ordeal, I can tell that it absolutely is, and it’s probably a cycle you want to avoid putting your employees through.
The password conundrum
Complex passwords are good, but often force silly work-arounds like writing them down. If you have your passwords written on post-it notes in your drawer (or worse, attached to your monitor), this isn’t the most secure approach, is it?
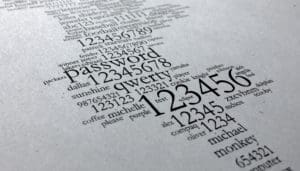
On the other hand, people can be amazingly simplistic, when it comes to creating passwords. The worst password lists have 12345 and password (yes, the word password) topping the lists every year. You don’t have to be a hacker genius to figure that one out, do you?
Many people end up using the same passwords over and over across the internet for simplicity’s sake, and with each breach, those passwords get leaked. It means your regular password is probably floating around the internet somewhere, just waiting for someone with nefarious intent to pick it up and enter your company network using the stolen credentials.
By bringing in that second factor, you can limit the harm done by stolen credentials. If you are using an approve/disapprove service, you should train your employees to change passwords immediately if someone is trying to make a change that’s not them. You could even have a protocol to force this to happen.
Two-factor isn’t foolproof of course, but it does offer you a simple way to protect against stolen (or guessed) credentials without putting an undue burden on your users.
Photo: Mark Burnett on Flickr. Used under CC 2.0 license.

