 It took a long time, but I finally started changing my passwords on a regular basis. Previously, I viewed a familiar password as akin to Mom’s mac and cheese: easy comfort for the cyber soul.
It took a long time, but I finally started changing my passwords on a regular basis. Previously, I viewed a familiar password as akin to Mom’s mac and cheese: easy comfort for the cyber soul.
A hacker would never breach my system, I reasoned. I’m a journalist, not a Fortune 500 company — and I got lucky. I haven’t experienced any breaches, but prevention is always the cheapest cure.
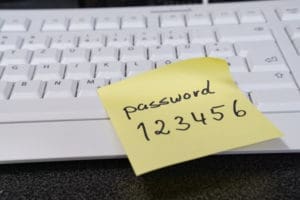
For the forgetful — and hackers — there’s nothing more comforting than an easy password. Where those two opposite trajectories collide, is where there are problems.
MSPs and password security
MSPs have a role and vested interest in keeping these two trajectories from colliding. There’s even an opportunity to add a layer of value to a customer’s service package while compensating for the extra expertise.
Some persuading may be in order because passwords seem like one of the simplest components of the entire ecosystem. Why should customers pay you for password expertise when all they need to do is set their password to Basketball123 and be done with it? Unfortunately, in a world filled with cyber threats, nothing is that easy.
As long as passwords are a security tool, MSPs need to offer password management as either part of a standard service package or an upgraded one. Biometrics, voice, and other access tools offer promise, but, for now, the password reigns supreme. Every new year arrives with the promise of passwords being dethroned, but 2020 is here and guess what? Passwords are too.
As Animation Express observed:
“MSPs often promise fantastic security and all sorts of bells and whistles to gain your business, but unfortunately, that does not include smart password management for most of its customers.”
MSPs should offer smart password management as part of their service packages. Smart management is as easy as 123, and no password management is as troublesome as 123456, which Splashdata revealed to be the top password of 2019.
For those who wanted to mix it up a bit, coming in at number two was 123456789, and rounding out the top three was qwerty.
Having customers who use passwords like that, might as well put a bullseye target on the system for a hacker. Hackers still often rely on password “spraying” to crack a system because it works.
In reaching out to experts about what can be part of a smart password plan, we came up with some best practices that are worth following:
Change default settings
You may think that the password printed on the back of the new router you installed is impenetrable. But that “stuffedbear606” password is probably on a hacker’s radar. Bad actors have a way of obtaining these default passwords, so why make it easy for them? Instead, set secure, random passwords filled with non-letter characters, to keep hackers guessing.
Microsegment
If you are not going to change the password from the default password (because you are managing thousands of different devices), then at least microsegment, particularly when it comes to mobile IoT units.
Schedule automatic password purges
More and more companies are turning to automatic purging programs that force someone to reset their password. Having a quarterly purge would ensure that someone doesn’t get lax with their password setting.
Offer a best practice training
Time is money, but so is a hacked network. There is a lot of value in having one of your technicians lead a 30-minute, once-a-year refresher class on how to improve password hygiene. Often, when someone is in a hurry and they need to reset their password, they choose “password” as their password, and don’t think about it. Persuade your customers to join a 30 minute training, to avoid password mishaps down the road.
Device audit
Depending on the complexity of a client’s network, you should plan regular audits of their connected devices. For instance, if a trucking company is one of your customers, you should make sure that all the connected devices in sales, parts, and accounting department are all on your radar. It might be easy to forget the greasy laptop or router near the service bay, but a routine scan for connected devices combined with regularly scheduled password purges will reduce the odds of a breach.
Off-cloud password storage is also a significant security step. Of course, you must watch your own house. MSPs with access to thousands of password credentials are becoming increasingly attractive targets for hackers.
With a combination of common-sense and forward-thinking and you’ll have a much more secure password regimen that will leave hackers frustrated. But it’s not as easy as 123123 (that’s #10 on the list!).
Photo: Angela Rohde / Shutterstock

