Category: Featured
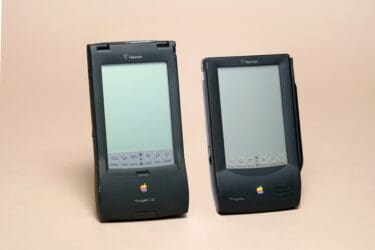
Tech Time Warp: An honest look back at the Apple Newton
The history of Apple is filled with greatest hits—but even its rare misses are worthy of retrospective examination. Take the Apple Newton, which received its first public demo on May 29, 1992, in Chicago at the Consumer Electronics Show. By...

Rising AI cost concerns create opportunities for MSPs
As the number of tokens consumed by artificial intelligence (AI) agents and applications continues to climb, organizations are paying much closer attention to cost. It feels like the conversation has shifted almost overnight. Not long ago, the focus was on...

Cybersecurity Threat Advisory: ClickFix attacks
Attackers are exploiting a critical vulnerability, tracked as CVE-2026-26980, in the Ghost Content Management System (CMS) to compromise more than 700 legitimate websites. Read this Cybersecurity Threat Advisory to reduce risk for you and your clients. What is the threat?...

IoT threats in 2026: The blind spot MSPs can’t afford to ignore
Cybersecurity experts have warned about IoT threats for years. But as the IoT security landscape continues to expand and evolve, so do the risks—making this a topic worth revisiting. While solutions to secure IoT devices exist, MSPs must stay immersed...

What competitor websites tell you about service gaps in the market
Here is something I have noticed after years of helping MSPs build outbound sales programs: most of them think they know their competitors. They really don’t. What they have is a collection of impressions: Some gossip from a disgruntled sales...

Cybersecurity Threat Advisory: Exchange on-premise OWA vulnerability exploited
A Microsoft Exchange Server Outlook Web Access (OWA) spoofing vulnerability, tracked as CVE‑2026‑42897, is actively being exploited in the wild. This issue affects Exchange Server 2016, Exchange Server 2019, and Exchange Server Subscription Edition across all update levels. Continue reading...

Tech Time Warp: Was Java too much of a good thing?
This edition of Tech Time Warp takes us back to 1995—the public debut of Java, the legendary “Write Once, Run Anywhere” programming language—and a textbook example of the security perils of ubiquitous technology. The birth of Java On May 23,...

Inside IT: Opportunities MSPs should miss
A global survey of 400 IT leaders provides some significant insights into the types of IT expertise that organizations might be willing to consider relying on a provider of IT services to provide. Conducted by the Linux Foundation, the survey...

Cybersecurity Threat Advisory: Cisco Catalyst SD-WAN zero day vulnerability
An authentication bypass zero-day vulnerability, tracked as CVE-2026-20182 with a maximum CVSS score of 10.0, has been identified in Cisco Catalyst SD-WAN Controller and Manager. The vulnerability allows unauthenticated attackers to gain the highest level of administrative access to affected...

Patch management: The basics still matter
Patching is such a core part of MSP DNA that it’s easy to overlook. I’ve talked with many MSP owners who get pulled into the latest, most urgent cyberthreats—only to lose sight of the basics: patching. Patching is the cybersecurity...

