Category: Security

Ask an MSP Expert: How can an RMM automate security offerings?
Q: I have heard that adding an RMM tool can improve delivery of our managed security services offering for customers, specifically through automation. How can an RMM tool do this? If the new situation that MSPs and their clients find...

Tech Time Warp: Klez.H virus confuses with spoofed emails
It is possible the creator of Klez was rather indecisive. The malware, which confounded computer users in the early 2000s, was all at once a virus, a worm, and a Trojan horse. Basically, Klez contained every trick in the hacker...

Cybersecurity Threat Advisory: Office 365 MFA Bypass Phishing Attack
Advisory Overview A new type of Office 365 Phishing attack uses the legitimate Microsoft login page to bypass multi-factor authentication. The attack grants certain permissions to threat actors, compromising the target user’s account and its data. SKOUT advises businesses to...
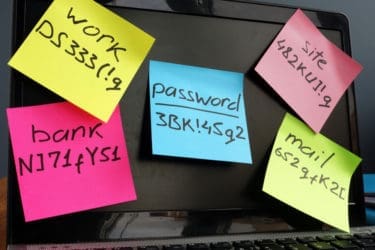
Passwords in a pandemic
World Password Day was celebrated earlier this month with some sobering statistics that may have people rethinking the use of their daughter’s middle name or favorite Italian dish as the basis for all of their security. MSPs can only hope...

Jumping the air gap
With everyone wearing masks and wincing each time someone coughs, airborne viruses have captured the attention of the world. Your client’s network can’t catch COVID-19 from a sneeze, but it can catch other airborne viruses.

SMBs’ security vs. headcount decision creates MSP opportunity
Business executives in the wake of the COVID-19 pandemic are now wrestling with some critical decisions that are likely to define their relationships with managed service providers (MSPs) for many years to come. A survey of over 1,000 business decision...

Protecting remote workers from COVID-19 phishing attacks
Q: One of our customers’ remote workers recently clicked a phishing link. While we were able to prevent the attack from ultimately being successful, this is quite concerning, especially since remote workers are not within a secured network. How can...

Tech Time Warp: Hack shuts down PlayStation Network for 3 weeks
Video games have been a godsend during the COVID-19 pandemic, providing those “staying at home” with diversion and a chance at safe social interaction (Animal Crossing, anyone?). It’s worth remembering, however, that even the big guys in digital gaming and...

Protecting the cyber-classroom from its users
Last week, we discussed how vulnerable online classrooms can be to attempts from external actors and what routes they may take to get there. But as is the case most of the time in cybersecurity, the easiest entry method for...

Beware as COVID-19 is bringing out spammers and scammers
I was going through one of my email accounts the other day and I noticed a bunch of 1990s-style spam emails. There was the promise of sharing some uncollected inheritance with me from some deceased African royalty if I only...

