
Expert views on closing the cybersecurity talent gap for MSPs
The cybersecurity talent shortage in the workforce presents a direct cybersecurity threat. Statistics from the National Institute of Standards and Technology (NIST) paint a grim picture: By 2025, a lack of talent or human failure will be responsible for over...

Survey: Demand for cloud cost control expertise is on the rise
The volume of applications deployed in the cloud continues to increase steadily. More organizations are looking to contain costs but are finding they lack the skills and expertise needed. A survey of over 400 cloud and data decision-makers conducted by...

Analyzing the latest Ivanti-linked CISA breach
Another day passes, another cyberattack strikes. This time, a recent incident impacted a major U.S. government entity known as the Cybersecurity and Infrastructure Security Agency (CISA). Back in February, CISA officials discovered that two of its internal computer systems were compromised by...
Sales & Marketing

Your MSP website doesn’t need to be catchy
IT is one of the most in-demand business services in the world. There are thousands and thousands of managed service providers (MSPs) out there. The struggle in every crowded industry is to stand out. The IT world is no exception....

Obliterating three MSP marketing misconceptions
The marketing industry is a fascinating one. When you look up tips from experts, you’ll see all kinds of misconceptions, myths, and conflicting information. However, this isn’t because the experts don’t know what they are talking about. For one, the...

Tip Tuesday: Utilize social proof to elevate your MSP’s market position
Managed service providers (MSPs) must stand out from dozens of competitors if they want companies to use their software service. Social proof is a great way to provide insight into your company’s offerings and elevate your market position. Tapping into...
Security

Cybersecurity Threat Advisory: RCE vulnerabilities in HPE Aruba Networking devices
HPE Aruba Networking has disclosed that critical remote code execution (RCE) vulnerabilities are impacting multiple versions of ArubaOS. Out of the ten vulnerabilities found, four pose critical risks of unauthenticated buffer overflows in various services. Read this Cybersecurity Threat Advisory...
MSPs are on the front lines of fighting deepfakes
Alarm bells went off in board rooms and C-suites across the globe last fall when an executive at a Hong Kong company was duped by deepfakes into wiring $25 million to criminals. According to CNN: A finance worker at a...
Better Business

Minding the cybersecurity talent gap for MSPs
We have reported extensively on the cybersecurity talent shortage plaguing the industry. The shortage is more than just a personnel issue though, it represents a serious cybersecurity problem. For instance, a Gartner report says that by 2025, half of all...

Generative AI is a game-changer for how MSPs demonstrate value
Customers like to have a clear understanding of what’s going on. MSPs hold more than enough data to let customers know what is going on with their services. However, they struggle to transform this data into a useful form that...
Tech Insight

AI adoption creates additional cybersecurity opportunities for MSSPs
The adoption of generative artificial intelligence (AI) by organizations continues to rise. Therefore, there is a strong need to make sure the data being shared with these platforms is secure. The National Security Agency (NSA), in collaboration with multiple security...
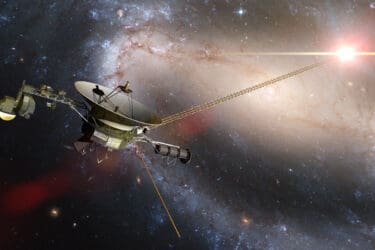
Tech Time Warp: Voyager’s nearly 47 years of technology brilliance
In this edition of Tech Time Warp, we take a look at how, for almost 47 years, NASA’s Voyager 1 spacecraft has transmitted the amazing secrets of the universe back to Earth. Along with that, the news that engineers had...

Survey sees an increase in MSP IT spending
While no one knows for certain what percentage of the trillions of dollars spent on IT might be accounted for by managed service providers (MSPs), recent research suggests MSP IT spending is growing at a significant rate. A survey of...







